Posts by David Stevenson
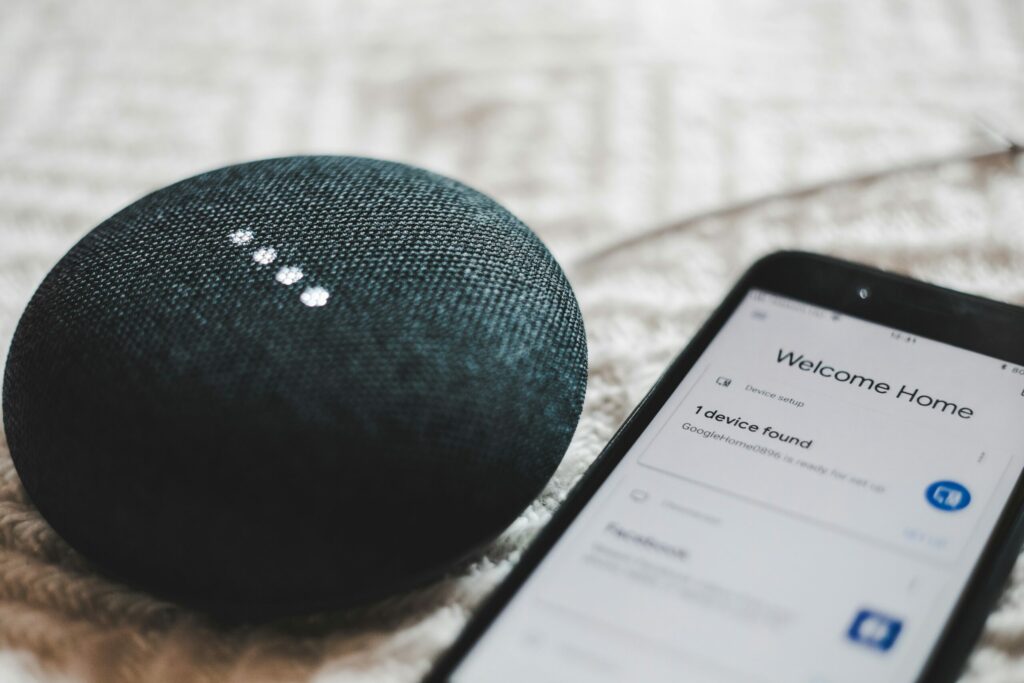
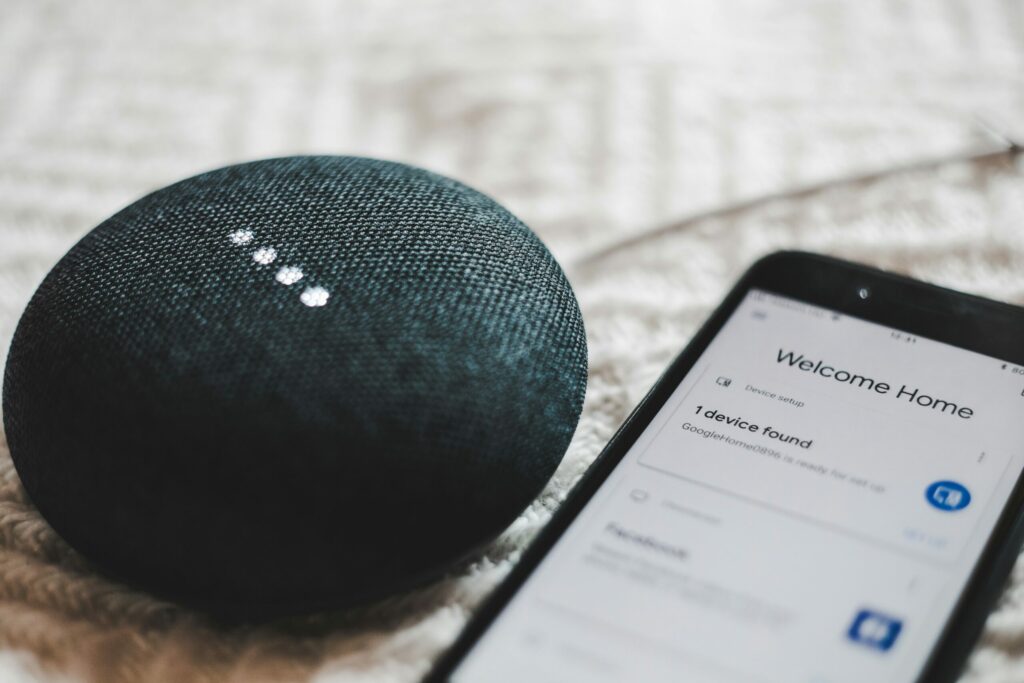
7 Important Considerations Before You Buy Smart Home Tech
Smart homes seem like something straight out of a sci-fi movie. They have lights that respond to your voice commands and thermostats that auto-adjust. Not to mention robot vacuums that clean your floors while you relax. It’s all very tempting. But before you rush out and buy the newest gadget, there are some crucial considerations.…
Read MoreWhy Continuous Monitoring is a Cybersecurity Must
Imagine this: you leave your house for vacation. You live in a shady neighborhood but feel confident your locks are secure, but you also don’t checkthem daily. Are they really locked and safe? A tiny crack or hidden weakness could have occurred. It’s a disaster waiting to happen. That’s the risk of neglecting continuous cybersecurity…
Read MoreA Simple Guide to the Updated NIST 2.0 Cybersecurity Framework
Staying ahead of threats is a challenge for organizations of all sizes. Reported global security incidents grew between February and March of 2024. They increased by 69.8%. It’s important to use a structured approach to cybersecurity. This helps to protect your organization. The National Institute of Standards and Technology (NIST) created a Cybersecurity Framework (CSF).…
Read MoreHot off the Digital Presses… Learn About Microsoft Copilot for Finance
Microsoft Copilot has been heading up the business AI charge. It’s used in Word, Excel, Edge, Windows, and more. This genAI-powered app is also showing up invarious function-related activities. The latest of which is finance processes. Microsoft Copilot for Finance is a game-changer. It injects the power of next-generation AI into the heart of your…
Read MoreiPhone Running Slow? Speed It up with One of These Tips
Let’s face it, iPhones are amazing devices. But even the sleekest, most powerful iPhone can succumb to the dreaded slowdown. Apps take forever to load and scrolling feels sluggish. Pretty soon, simple tasks become frustrating ordeals. If your iPhone has gone from speedy sidekick to sluggish snail, don’t despair! We are sharing some easy tips…
Read MoreIs Your Business Losing Money Because Employees Can’t Use Tech?
Shiny new tech can be exciting! It promises increased efficiency, happier employees, and a competitive edge. It’s also necessary to stay competitive in today’s technology-driven business world. But that promise can turn into a financial nightmare if you neglect two important things. These are employee training and change management. You can end up losing money…
Read More10 Easy Steps to Building a Culture of Cyber Awareness
Cyberattacks are a constant threat in today’s digital world. Phishing emails, malware downloads, and data breaches. They can cripple businesses and devastate personal lives. Employee error is the reason many threats get introduced to a business network. A lack of cybersecurity awareness is generally the culprit. People don’t know any better, so they accidentally click…
Read MoreWhat Were the Coolest Consumer Products Showcased at CES 2024?
The annual Consumer Electronics Show (CES) was an exciting one this year. It left us with a mind-blowing glimpse into the future of technology. CES 2024 showcased a smorgasbord of cutting-edge gadgets. Including transparent TVs and robot pet buddies. These gadgets promise to revolutionize our homes and the way we interact with the world. With…
Read MoreSmart Tips for Building a Smart Home on a Budget
Imagine a world where your lights turn on automatically as you walk in the door. Your coffee starts brewing before you even crawl out of bed. A simple voice command adjusts the temperature to your perfect setting. This is no longer just something out of a sci-fi movie. Today’s smart technology seamlessly integrates with your…
Read MoreGuide to Improving Your Company’s Data Management
Data is the lifeblood of modern businesses. It fuels insights, drives decision-making, and ultimately shapes your company’s success. But in today’s information age, data can quickly become overwhelming. Scattered spreadsheets, siloed databases, and inconsistent formatting. All these create a data management nightmare. This hinders your ability to leverage this valuable asset. Let this guide serve…
Read More